Humanising Cryptographic Authentication
One of the most overloaded terms in the digital world is identity; this means it is difficult to strongly establish the Digital Me – Who am I in the Digital World? Security is solved. Humanising cryptographic authentication is the key to solving identity.
The identity ecosystem, and especially the digital identity ecosystem needs 3 specific frameworks (the 3 ‘A’s): Authentication, Authorisation and Attributes.
Authentication is the most critical one, as this is what establishes the Digital Me, establishing (or rather providing enough confidence to establish) “Who am I in the digital world?”.
Ironically, the digital world still relies on passwords as the authentication framework in many instances and has been doing so since 1961, when passwords were first used at MIT for the CTSS (Compatible Time-Sharing System). This makes the password one of the longest-surviving technologies.
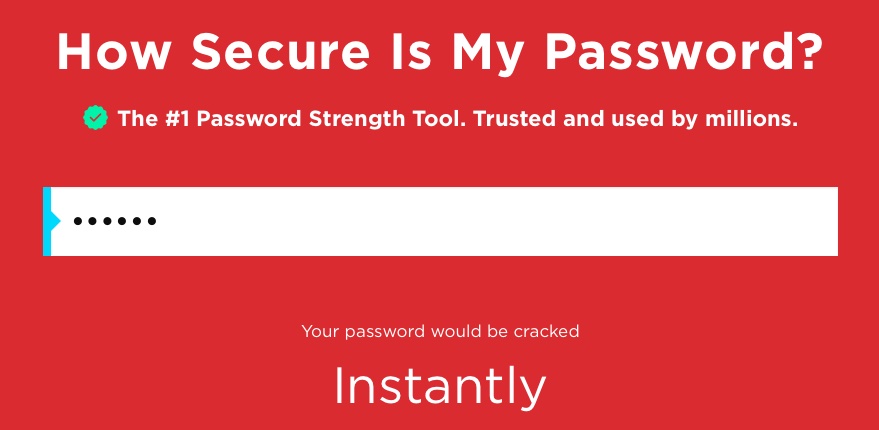
Some of the statistics around passwords are mind-boggling and amusing at the same time: there are more than 300 billion passwords in use, 81% of data breaches in the digital world are somehow related to passwords and the most popular password in the digital world is 123456 (which can be cracked instantly – see https://www.security.org/how-secure-is-my-password/
Authentication has come a long way, even if there is still a lot of reliance on passwords as the authentication mechanism. From knowledge-based authentication (e.g., passwords) to possession-based (e.g., OTPs) and then to inherence-based (e.g., biometrics). If we look into the long journey authentication technologies have taken over the six decades (yes, it has been more than six decades since the use of passwords as the pioneering technology for authentication), we can identify that some of the key characteristics have remained unchanged:
- The user has been kept active in the authentication process, even if there are realisations that the user is the weakest link in the chain.
- Authentication as a barrier to service access: The user wants the service, but they have to go through the authentication barrier – there is a mismatch between what the user wants and what the user has to go through. The authentication is not invisible.
- Authentication happens at the start of a service session, and it is almost assumed that all the contexts will remain the same throughout the session and beyond. Authentication is generally not continuous in the majority of scenarios.
- Most importantly, the authentication process is not humanised. The authentication process is used by machines but is expected to be participated in by humans.
There are realisations of these elements around authentication within the industry and there have been attempts to address these in the last few years. Two key themes have emerged in the evolution of authentication technology:
- Risk-based authentication
- Cryptographic authentication
Risk-based authentication has been used primarily for authentication augmentation to add additional confidence to the primary authentication process and is mostly used in the financial eco-systems including banking, fintechs, micro-lending domains and also within BNPL services.
Humanising cryptographic authentication has been at the forefront recently; many successful and popular approaches including FIDO2/WebAuthN, Passkeys, SSI/Decentralised Identity and some attempts to use key-sharing are there too. The wallet ecosystem has used the approach as well, including crypto wallets, sometimes driven through Blockchain/DLT realisations.
There is absolutely no argument on the security aspects of cryptography for authentication, but we know the balance between security and convenience is critical for the technology to have a world-changing impact, and when given a choice between convenience and security – the users generally lean towards convenience, sometimes subconsciously. Cryptographic keys are for machines and not for humans.
When Tony Robbins said: “Identity is this incredible invisible force that controls your whole life. It’s invisible like gravity is invisible, but it controls your whole life.”, he was talking about Organic Identity – he was talking about humanised identity. On almost similar lines, when Steve Jobs said, “Technology should either be beautiful or should be invisible”, he was likely referring to the humanisation of technology.
Passkeys have been a hot topic within the authentication space recently, let’s look into them, how do they work? A challenge message is sent to the device, which is then cryptographically signed by the key securely stored in the secure element of the device and the signature is then validated to assert the authentication. Let’s go back to 1991, the SIM is invented, and used by all GSM-based mobile devices. How does the authentication in a SIM work? A random challenge is sent to the SIM to get signed and the signed response is validated by the mobile network operator. Sounds similar?
Cryptography has been at the core of mobile network technology for the last three decades, still, the cryptographic keys are invisible to the user – humanising it to a great extent. The SIM card (including the recent evolution into eSIM) contains cryptographic keys which are critical to the authentication of the user, through the possession and control of the SIM card; the “I” in the SIM is for ‘identity’ after all.
Most users are not even aware of the existence of the cryptographic keys, including the 128-bit Ki (authentication) key in the SIM, and that there are complex crypto dances going on to make the mobile network manage that identity. Added to that, the mobile network makes sure it knows if any changes have happened to the SIM – which is the cryptographic key manager.
If the SIM has been swapped, including if the user loses the mobile phone with the SIM, then the disablement of the SIM card – along with the cryptographic keys inside – is just a phone call away to the mobile operator’s customer service department.
Mobile Authentication employs cryptographic authentication reusing the critical asset – the SIM, in a humanised way. It may sound strange, perhaps radical, but the invisibility of technology, as popularised by Steve Jobs, is a humanising factor and has a critical security narrative. We can summarise it as “seamless” technology. Invisible and seamless humanised technology nicely balances the much sought-after twin dimensions of security and convenience. At Sekura, this is what we have been using for SAFrAuth, covering a large geographic footprint around the globe.
One important element of humanisation is “Identity inclusiveness”, where any of the 700+ mobile operators around the world can provide the humanised cryptographic authentication, as excluding any mobile operator is excluding the human subscriber of the operator. At Sekura, we believe “Identity for All” is critical for digital inclusiveness and for the betterment of societies including benefits management. Recently, we have demonstrated that it’s not just talk – we also walk the walk. For BSNL, a ‘smaller’ mobile operator in India, with approximately 114 million subscribers, we implemented the cryptographic mobile authentication with them within 10 days, including all the deployment, configuration, and integration and without any CAPEX investment from the MNO, all using the flexibility of the SAFr platform we have built.
Several risk-mitigation signals, invisible to the user, are also delivered alongside mobile authentication, like SIM-Swap, Call Forward, porting indication etc. which enhances the confidence for mobile authentication, and all delivered through the same SAFr API.
Let’s humanise cryptographic authentication – the SIM-based mobile authentication – SAFrAuth is already doing it.
With coverage across 5 continents, Sekura Mobile Intelligence is the leading global provider of mobile identity solutions, providing trusted, secure, and easy-to-consume solutions for ID verification, anti-fraud and secure online authentication use cases. Sekura works with established KYC, identity verification and risk data providers who have already integrated into leading global brands with demand for mobile identity solutions.
Through the integration of real-time mobile data into our partners’ existing services, we enable them to extend and enhance their customer offerings into new services, use cases and geographies through the adoption of SAFr, our single standards-based, mobile intelligence API.
To offer your customers the opportunity to benefit from our global mobile identity solutions, contact the Sekura team today.